TL;DR: A fresh look at IT safety with smartphones, a "reverse of control" approach, and P2P at center stage.
With the number of active smartphones approaching the size of the planet population, many companies advocate a "mobile-first" approach—including in security-related usage cases. However, due to factors specified as developer inertia and incremental updates to legacy systems, server-centric architectures inactive dominate technology stack decisions. erstwhile it comes to security, mobile devices are frequently relegated to a specified "second factor".
Despite crucial advancement in the field, including the shift towards "passwordless" security, this domain remains brimming with outdated clichés — from identity providers and firewalls to freely flowing access "tokens". As a result, safety incidents and their economical implications proceed to rise.
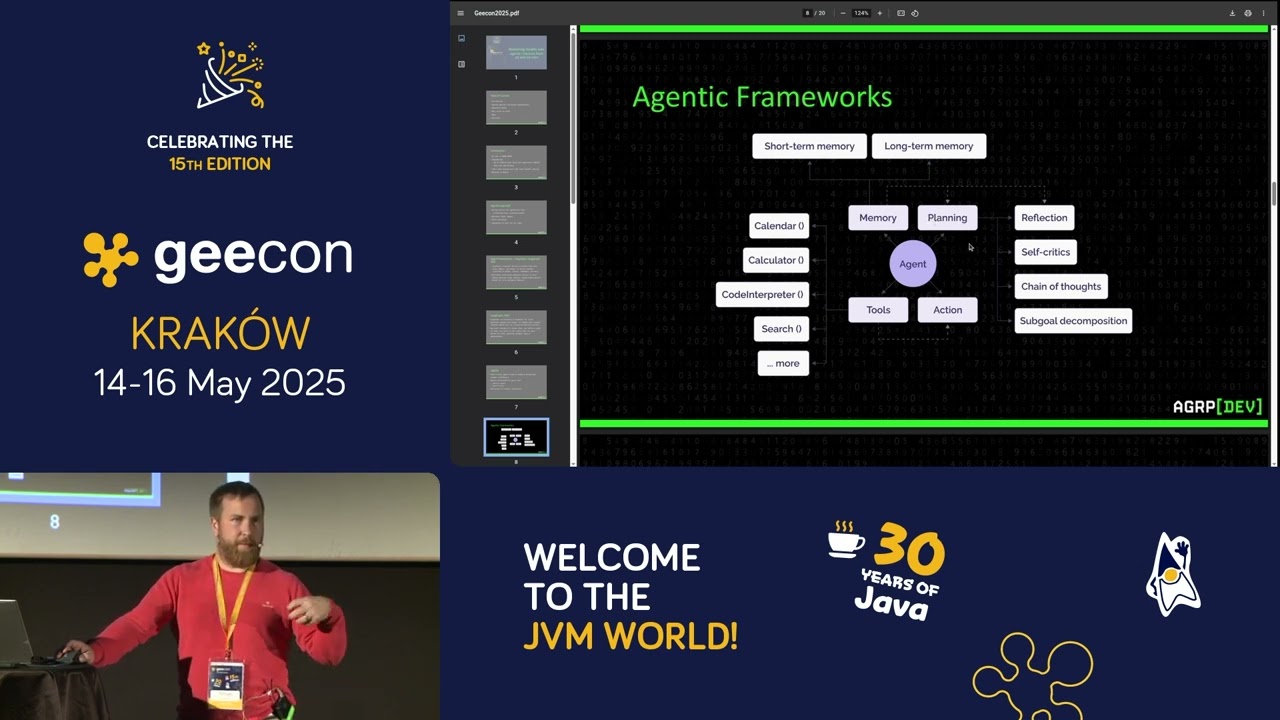
This talk offers a fresh position on security, placing the user and their smartphone at the center. We will research how modern smartphones—equipped with a variety of sensors and advanced safety technologies—can aid us weave a safety network far more resilient than existing solutions.
We’ll start by dissecting current safety and identity management technologies, identifying their weaknesses and breaking points. Then, we will distill best practices and item common pitfalls to avoid. The core of this talk will focus on how to leverage proven smartphone safety techniques—such as asymmetric cryptography, safe enclaves, and biometrics—and combine them with little commonly utilized elements (e.g., environmental data from sensors and P2P interactions) to form stronger safety chains than those typically available today. We will cover applicable usage cases, including authentication, identity verification, mitigating common attacks, and handling exceptional situations—such as losing your smartphone or another critical component of your safety chain. This discussion will dive into method details, providing applicable tips and example code.
This talk does not cover or advance any existing product. The ideas presented can be implemented in any programming language applicable to mobile and server development, including good old Java.